The United States government is considering going after ransomware attackers like it used to hunt pirates at sea, according to a Senate hearing on cyber with Pentagon officials.
Today, the Senate Armed Forces Subcommittee on Cyber held a hearing with three expert witnesses from the Department of Defense to explore how to tackle the rise in ransomware attacks that have threatened America’s national security and critical infrastructure.
Mieke Eoyang, Deputy Assistant Secretary of Defense for Cyber Policy, said that comparing the cybersecurity threats of today to the threats posed by pirates of auld was an “apt analogy,” albeit a complex one to maneuver in modern times.
“I’ve actually been thinking a lot about the development of international law and piracy as it relates to cybersecurity, and I think it’s a very instructive one for us as a nation” — Mieke Eoyang, Deputy Assistant Secretary of Defense for Cyber Policy
During his five minutes, Senator Mike Rounds reminded the panel that the US military used to take out pirates in foreign territories all the time.
He then asked the panel why the Pentagon couldn’t hunt down malicious cyber actors the same way it used to hunt down pirates at sea.
Eoyang noted that times had changed since the pirating days in early American history and that there would be “complicated legal issues” surrounding such an approach.
She also added that thinking about how we used to deal with pirates with regards to cybersecurity was “very instructive” for the US as a nation.
Here’s how the whole exchange went down:

Mike Rounds
“In the beginning years of our country, we made it very clear that when pirates would attack shipping that was vital to the United States […] we basically took them out — even though they had found a safe harbor in other sovereign countries” — Senator Mike Rounds
Senator Rounds:
“In the beginning years of our country, we made it very clear that when pirates would attack shipping that was vital to the United States, we actually created the Marine Corps, in a way, to actually go on out and find these private citizens who were acting as pirates, and we basically took them out — even though they had found a safe harbor in other sovereign countries.
“In doing so, we extended and recognized that the defense of our country included the defense of our assets. We did this using our, at that time, Department of the Navy and the Marines — I’m going to say the Department of Defense today.
“I think it still holds true with regards to cyberattacks, and I think the Department of Defense clearly has a role to play in extending and in protecting — and I think most citizens of the country believe that if someone from out of the country is going to attack us — either critical infrastructure, or in the case of ransomware, if there is a way for our Department of Defense to either stop the incoming attacks, or to respond accordingly outside of our country to those incoming attacks, would seem to be appropriate to do so.
“Recognizing that this is not normal just stealing of information and espionage, this is a demand for payment, or this is a direct attack on property within the United States.”
Senator Rounds then asked if his pirate analogy was applicable today in the face of ransomware attacks on critical infrastructure in the United States.
Eoyang replied that his analogy was “very instructive,” and that she had already been considering it.
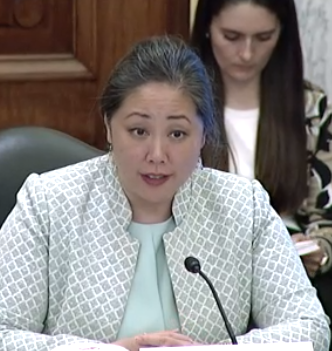
Mieke Eoyang
“I do think international law has evolved somewhat since the days of piracy […] and we need to be able to think about that analogy in the context of technology and the complicated legal issues that arise” — Mieke Eoyang, Deputy Assistant Secretary of Defense for Cyber Policy
Eoyang:
“Senator Rounds, I very much appreciate your analogy to piracy because I’ve actually been thinking a lot about the development of international law and piracy as it relates to cybersecurity, and I think it’s a very instructive one for us as a nation.
“One of the challenges that we saw with piracy is that territories at that time were either unwilling, or unable, to do anything about the threats that emanated from their territory.
“And I think this is a very important question for us to be asking now as we see the cyber actors who are operating outside the United States.
“Are they operating from a territory where the host nation is unable to be able to do anything about it? In which case we need to focus on how we build capacity, how we build relationships with allies and partners, how we ensure that they understand the severity of the problem and are willing to cooperate with us in bringing those perpetrators to justice as part of a whole-of-government effort.
“Or, in those cases where there are nations that are unwilling — unable is one thing, unwilling is another — and when they are unwilling, then that poses a diplomatic challenge and a national security challenge.
“And we have seen the president ask that question directly of a territory where we have seen a number of malicious cyber actors using as safe haven for their activity to victimize countries around the world.
“And to be very clear, that they have a choice to make about whether or not they are willing to do anything about this, and that they will be held accountable for being unwilling to do so.
“So, I think it’s an apt analogy [piracy] in this space. I do think international law has evolved somewhat since the days of piracy, or at least I hope so, and we need to be able to think about that analogy in the context of technology and the complicated legal issues that arise.”
Testifying alongside Eoyang in today’s hearing were expert witnesses Major General Kevin Kennedy, Director of Operations at the United States Cyber Command; and Rear Admiral Ronald Foy, Deputy Director for Global Operations at the Joint Staff.
The three witnesses submitted a joint written testimony, which you may read in full here.
“When they are unwilling, then that poses a diplomatic challenge and a national security challenge” — Mieke Eoyang, Deputy Assistant Secretary of Defense for Cyber Policy
Below are some excerpts plucked from their joint testimony:
- The recent Colonial Pipeline and JBS compromises have demonstrated ransomware’s potential to disrupt the everyday lives of Americans.
- Ransomware is a threat to our national security, and thwarting ransomware actors effectively requires a whole-of-government response that is coordinated with the private sector and our international partners.
- The list of American ransomware victims is long and grows each day, as the threat becomes more pervasive.
- Addressing the threat of ransomware will be a challenge. Part of this challenge is the increasingly blurry line between nation-state and criminal actors.
- We have seen some governments let government-employed hackers ‘moonlight’ as cybercriminals for personal benefit, which is not how responsible States behave in cyberspace.
- Our adversaries have also created permissive environments for criminal ransomware gangs, allowing them to operate from within their borders and shielding them from prosecution so long as they avoid targeting the host country’s businesses and government systems.
- This is sometimes evident in ransomware code, as gangs operating in Russia design their malware to avoid infecting computers where Russian is the default language.
- We continue to leverage the insights gained by operating on foreign networks to improve our cyber defenses, and we continue to strengthen our partnerships with the Federal Bureau of Investigation and the Department of Homeland Security in order to improve the cyber defenses of Federal, State, and local governments, as well as those of the private sector.
- Thus far, ransomware perpetrators appear to be financially motivated and therefore to have targeted private industry for financial gain. These are crimes.
- The Department stands ready to support our colleagues in the Federal Bureau of Investigation in their pursuit of these criminal actors. Further, the Department may provide assistance, when requested, to the Department of Homeland Security (DHS), which has the lead for protecting domestic critical infrastructure.
The entire hearing was about an hour long, and there were issues that the committee could not discuss publicly in an open hearing.
Prepping for a cyber pandemic: Cyber Polygon 2021 to stage supply chain attack simulation
‘Ransomware is quickly becoming a national emergency’ amid pandemic: CISA acting director testifies