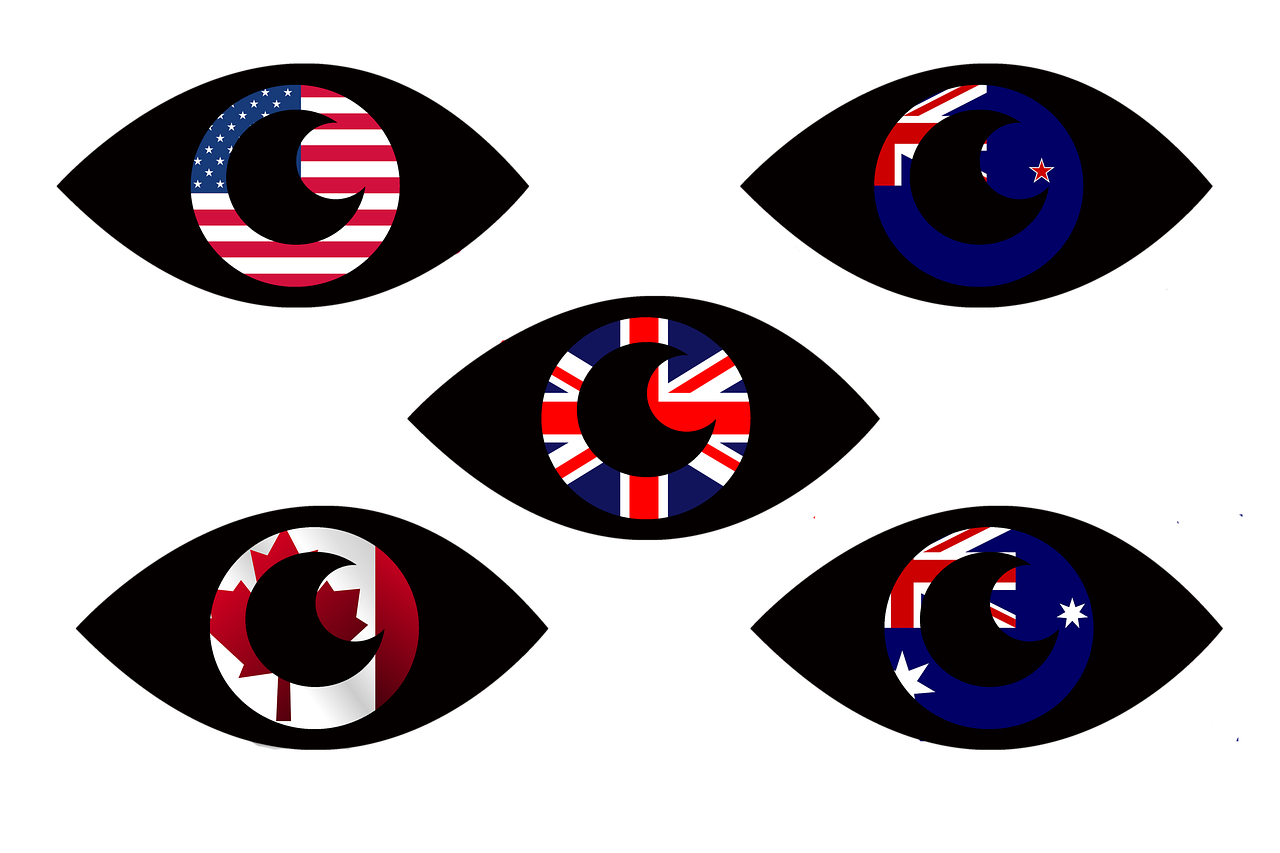
Citing malicious cyber activity as being “part of the Russian playbook,” countries belonging to the “Five Eyes” intelligence alliance issue a joint cybersecurity advisory urging critical infrastructure groups to prepare for Russian cyberattacks.
On Wednesday, the cybersecurity authorities of Australia, Canada, New Zealand, the UK, and the US issued a joint Cybersecurity Advisory (CSA) to “urge critical infrastructure network defenders to prepare for and mitigate potential cyber threats—including destructive malware, ransomware, DDoS attacks, and cyber espionage by hardening their cyber defenses and performing due diligence in identifying indicators of malicious activity.”
While the threat of Russian cyberattacks may be very real and imminent, false flag operations, faking the origins of cyberattacks, and conducting influence operations are all hallmarks of the Five Eyes, along with many other documented deception tactics.
“We know that malicious cyber activity is part of the Russian playbook” — Jen Easterly, CISA Director
With contributions from CrowdStrike, Google, LookingGlass Cyber, Mandiant, Microsoft, and Secureworks, the CSA is meant to warn “organizations that Russia’s invasion of Ukraine could expose organizations both within and beyond the region to increased malicious cyber activity” coming from the Russian government itself or other non-State cybercrime groups.
“We know that malicious cyber activity is part of the Russian playbook, which is why every organization – large and small – should take action to protect themselves during this heightened threat environment,” said US Cybersecurity & Infrastructure Security Agency (CISA) Director Jen Easterly, in a statement on Wednesday.
Easterly used the the same type of “Russian playbook” rhetoric that more than 50 former intelligence officials used when they smeared the accurately reported NY Post story about Hunter Biden’s emails as having “all the classic earmarks of a Russian information operation” just before the 2020 presidential election.
“Evolving intelligence indicates that the Russian government is exploring options for potential cyberattacks” — Joint Cybersecurity Advisory, April, 2022
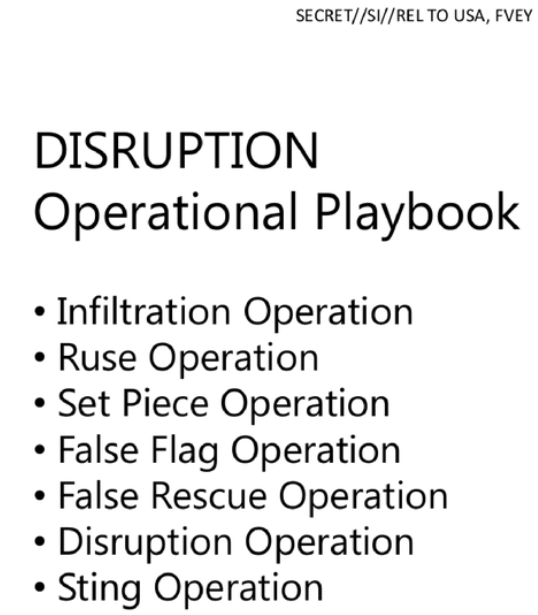
While the CISA director claims “malicious cyber activity is part of the Russian playbook,” she doesn’t mention that “False Flag Operations” are part of the Five Eyes’ actual playbook.
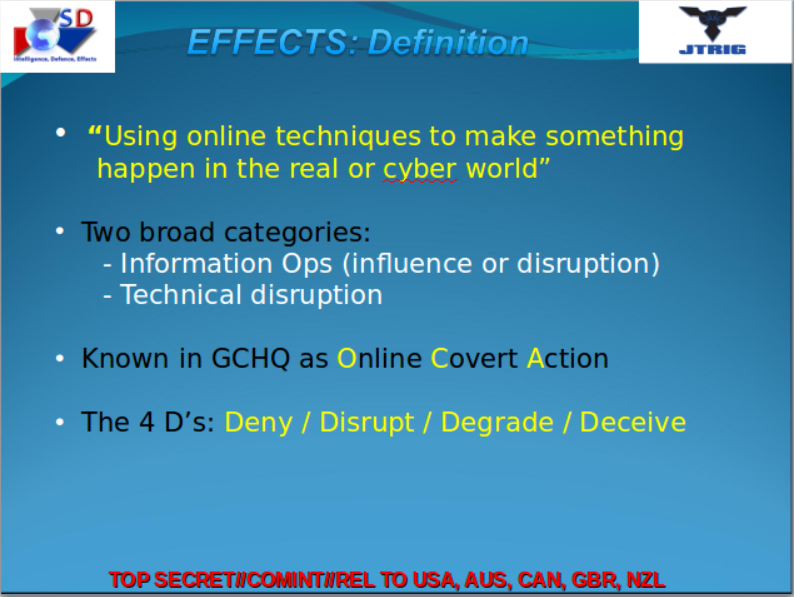
In February, 2014, journalist Glenn Greenwald published “The Art of Deception: Training for Online Covert Operations,” which was a training manual used by the British spy agency, GCHQ, and shared with the rest of the Five Eyes alliance.
The GCHQ’s Joint Threat Research Intelligence Group (JTRIG) playbook lists false flags, infiltration, and disruption among its many tactics of deception.
JTRIG’s “Online Covert Actions” include deploying the 4 D’s — Deny, Disrupt, Degrade, Deceive — while “using online techniques to make something happen in the real or cyber world” through both influence operations and technical disruption.
According to an NBC exclusive in 2014, British intelligence was reported to have launched a DDoS attack – the same type of attack that the Five Eyes are now saying Russia will likely conduct – on “Anonymous hacktivists,” thus becoming the first known Western government to have conducted such an attack.
And while the Five Eyes countries are pushing the narrative to blame Russia for any future cyberattacks on critical infrastructure, it’s worthy to note that US intelligence has been capable of faking the origins of cyberattacks since at least 2015.
“Marble is used to hamper forensic investigators and anti-virus companies from attributing viruses, trojans and hacking attacks to the CIA” — WikiLeaks Vault 7, 2017
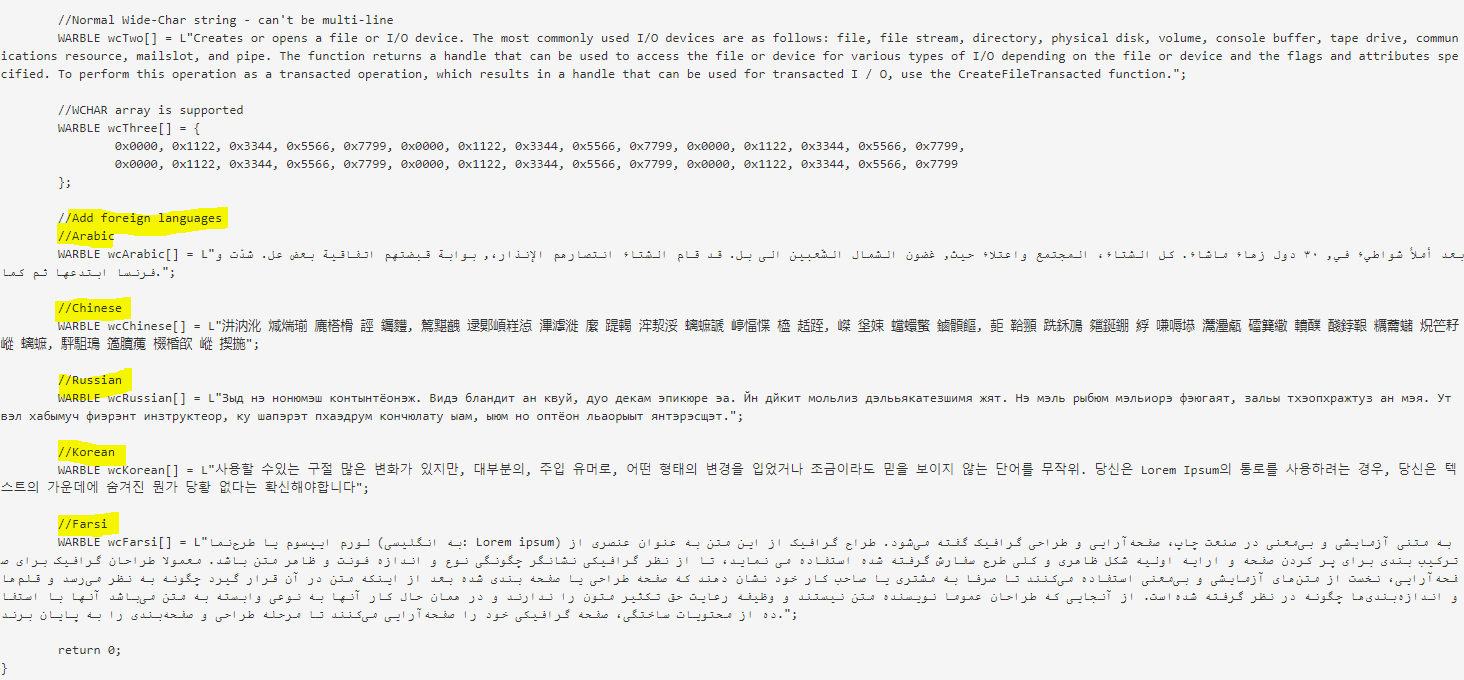
Among the many CIA hacking capabilities published by WikiLeaks in March, 2017, Vault 7 describes a CIA tool known as “Marble” that can confuse the true origins of a cyberattack — leading forensic investigators to the wrong conclusions.
According to WikiLeaks:
- Marble is used to hamper forensic investigators and anti-virus companies from attributing viruses, trojans and hacking attacks to the CIA.
- Marble does this by hiding (“obfuscating”) text fragments used in CIA malware from visual inspection.
- This is the digital equivalent of a specialized CIA tool to place covers over the English language text on US-produced weapons systems before giving them to insurgents secretly backed by the CIA.
According to WikiLeaks:
“The source code shows that Marble has test examples not just in English but also in Chinese, Russian, Korean, Arabic and Farsi.
“This would permit a forensic attribution double game, for example by pretending that the spoken language of the malware creator was not American English, but Chinese, but then showing attempts to conceal the use of Chinese, drawing forensic investigators even more strongly to the wrong conclusion, — but there are other possibilities, such as hiding fake error messages.”
“Russia’s invasion of Ukraine could expose organizations both within and beyond the region to increased malicious cyber activity” — Joint Cybersecurity Advisory, April, 2022
The next big cyberattack on critical infrastructure may very well come from Russia, as the Five Eyes countries warn.
But no matter the country, spy agencies will lie if it means achieving their goals, and they will tell the truth if it furthers their agenda.
Like any spy ring, the Five Eyes’ modus operandi is deception, which includes false flags, influence operations, and faking the origins of cyberattacks.
If a cyberattack were to cripple your nation’s critical infrastructure today, and your government told you it came from Russia, would you believe them?
“If cyberthreats continue without mitigation, governments will continue to retaliate against perpetrators (actual or perceived), leading to open cyberwarfare, further disruption for societies and loss of trust in governments’ ability to act as digital stewards” — Global Risks Report, WEF, 2022
Wednesday’s CSA builds upon the March 21, 2022 White House warning that “Russia could conduct malicious cyber activity” against America’s critical infrastructure “as a response to the unprecedented economic costs we’ve imposed on Russia alongside our allies and partners.”
In January, the World Economic Forum (WEF) published its Global Risks Report 2022 warning that retaliations to cyberthreats — whether actual or perceived — could lead to open cyberwarfare.
“If cyberthreats continue without mitigation, governments will continue to retaliate against perpetrators (actual or perceived), leading to open cyberwarfare, further disruption for societies and loss of trust in governments’ ability to act as digital stewards,” the WEF report reads.
If the unelected globalists at the WEF prove to be prophetic in their assessment, it would mean that governments wouldn’t need confirmation of an actual perpetrator before retaliating — just a perceived one.
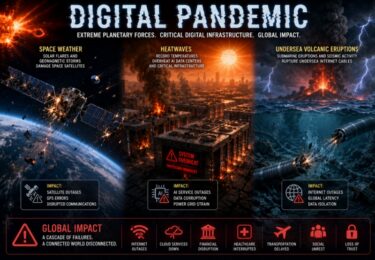
“We all know, but still pay insufficient attention to, the frightening scenario of a comprehensive cyber attack, which would bring a complete halt to the power supply, transportation, hospital services, our society as a whole” — Klaus Schwab, WEF, Cyber Polygon 2020
For the past few years, the WEF and partners have been prepping for a cyber pandemic that would wreak havoc over all of society due to cyberattacks on critical infrastructure, just as the Five Eyes countries warn.
Speaking at Cyber Polygon 2020, WEF founder Klaus Schwab warned:
“We all know, but still pay insufficient attention to, the frightening scenario of a comprehensive cyber attack, which would bring a complete halt to the power supply, transportation, hospital services, our society as a whole.
“The COVID-19 crisis would be seen in this respect as a small disturbance in comparison to a major cyber attack.”
This year, the WEF will once again be supporting the Russian-based annual Cyber Polygon cybersecurity training exercise on July 8, 2022 with a focus on “digital resilience in the cloud age.”
Discussions coming out of last year’s edition concluded with the desire to immunize the internet, demonize cryptocurrencies, and prop-up centralized systems of governance through a closer merger of corporations and States (public-private partnerships).